Sovereign Collaboration: The First Line of Modern Defense
In a world where the navigation system of an aircraft carrying the president of the European Commission can be jammed, forcing the pilot to use paper maps for landing, the importance of sovereign collaboration solutions for defense organisations is clear.
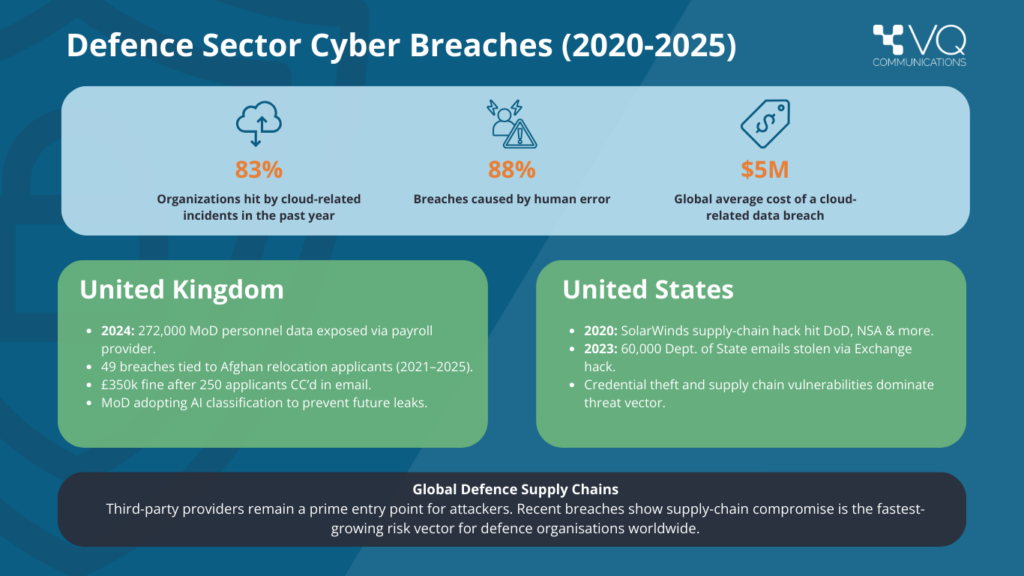
Nation-state cyber threats have risen sharply, with 90,000 of the cyberattacks faced by the UK over the past two years believed to be state-linked. Other key features of today’s defense communication threat landscape include:
Dependency on foreign cloud providers, with public cloud, commercial telecoms, and foreign-owned software creating backdoors in some cases.
Insider threats and data leaks, which are especially prevalent when granular permissions and effective secure communication protocols are lacking.
Understanding what it takes to achieve secure defense communications, and the real-world risks organisations need to address, are the first fundamental steps in levelling up your collaboration capabilities.
Defense is not the only space in which secure, sovereign collaboration is needed urgently. In this new series, we will also explore the importance of these capabilities for governments, financial services, and enterprises. But first, let’s take a closer look at what defense organisations are up against.
Gaining Situational Awareness
The threat landscape for defense organisations is shifting, and the increasing volume and sophistication of nation-state cyberattacks is one of the main causes.
Nation-state Cyberattacks
In the past, nation-state cyber activity was focused on espionage – principally the interception of military plans, details of trade negotiations, and other intellectual property. But alarmingly, disruption and sabotage have become priorities for nation-state actors.
From energy grids to transport hubs, we are seeing various types of critical infrastructure be targeted by state-backed cyberattacks with the goal to corrupt, disable, or destroy the systems behind them. Unsurprisingly, defense organisations are also facing an uptick in attacks designed to infiltrate and undermine their operations.
These state-sponsored campaigns are deployed at a global scale, and are often disguised as criminal activity by using attacks like ransomware. Because the motives behind these acts are blurred, defense organisations must adopt platforms that are secure-by-design, and assume that any attack could be strategic.
Dependency on Modern Cloud Providers
With global hyperscale cloud providers dominating the market, this concentration has presented critical points of failure that can lead to outages for millions of entities sharing the infrastructure. They also run on vast, opaque supply chains that are extremely difficult to secure end-to-end, drastically limiting assurance and control.
Data residency and movement present another major concern when using non-sovereign communications systems, with information often moved across borders even when the service is described as ‘regional hosting.’ Load balancing is one of the reasons this might be done, and often without the customer having full visibility.
Legal and jurisdictional pressure points can also undermine supposedly ‘secure cloud solutions’, regardless of how secure they are at a technical level. In a situation where geopolitical tensions flare between the user’s home nation and that of the cloud provider, a complete communications blackout is possible.
For a defense organisation, being caught up in a commercial data breach or downtime caused by geopolitical tensions could have catastrophic repercussions – including outages during critical operations.
Self-hosted conferencing with sovereign control is essential. Defining one of the most secure deployment models: an air-gapped system – completely isolated from external networks.
Watch as we explain what an air gap truly means and why it matters:
Insider Threats and Data Leaks
Today, if sovereign communications and role-based access capabilities are not in place, a single insider can compromise a defense organisation’s classified information and systems.
Vulnerable cloud-based collaboration tools have widened attack surfaces, and at the same time, deliberate insider threats are becoming as common as accidental leaks. The sheer volume of sensitive data handled by defense players – which often sprawls across multiple systems – has only added weak points for insiders to exploit (or misconfigure).
The emergence of tools like AI-powered data exfiltration are set to make insider threats an even greater concern for the industry, equipping individuals with the ability to gather and analyse massive amounts of data almost instantly. Capabilities like this are making insiders both more dangerous and harder to detect, regardless of skill level.
Real-world Cases
We have already witnessed many high-profile instances of the damage that can be caused when organisations rely on cloud-based or third-party systems without effective sovereign collaboration. Misconfiguring in shared cloud platforms can expose sensitive defense documents – a risk that also applies to collaboration platforms if not sovereign and self-hosted.
Third-party Breach
Underlining why defense organisations need to extend their sovereign collaboration frameworks beyond in-house systems, approximately 270,000 current and former military personnel were impacted by an indirect breach of the UK Ministry of Defense (MOD). In 2024, a third-party payroll system was compromised, disclosing names, addresses, and bank details.
State-sponsored API Attack
Spanning the end of 2024 and the beginning of 2025, the Treasury Department experienced what it called a ‘major cybersecurity incident’ when a state-sponsored actor breached a BeyondTrust cloud-based platform.
The compromised API key revealed treasury workstation data and put other government departments at risk, highlighting the potential domino effect caused by a compromised cloud supply chain.
How is the Defense Sector Responding?
Regardless of sector, organisations worldwide are recognising the importance of sovereign collaboration capabilities. In 2024, the global sovereign cloud market was valued at $96.77 billion, and is now projected to reach $648.87 billion by 2033.
When we look at the defense space specifically, initiatives like the transatlantic co-operation between defense organisations in the UK, the U.S., and Australia stand out. This joint operation is focused on the development of sovereign cloud infrastructures for secure data sharing.
At VQ Communications, we have enhanced the collaboration capabilities of a US Department of Defense (DoD) agency, providing the organisation with a secure video and audio-conferencing platform. The team also enabled a major player in the European defense industry to implement a highly secure sovereign conferencing service, protecting the operations of more than 200,000 users.
A major trend our experts have reported in the defense sector is a widespread shift toward self-hosted infrastructure. The goal of this is to improve data security while simultaneously ensuring compliance with complex sovereignty regulations.
Take a Tailored Approach
With a variety of regulatory, security and other factors to consider depending on jurisdiction, a tailored approach to sovereign collaboration is highly advantageous in the defense world. The right solution will not only be compliant and more resilient, but it will also be mission-aligned.
We are intimately familiar with the unique workflows and communication patterns defense organisations use, and VQ Conference Manager is proven in defense environments worldwide. From European defense organisations with 200,000+ users to US DoD agencies, we lead the charge in sovereign communication.
Discover how VQ can help your teams collaborate securely, at scale here.
Further blog articles that may
be of interest to you:
VQ Conference Manager Trials
VQ Conference Manager Trials This blog provides administrators with an overview on how to best proceed with trials of VQ Conference Manager and DMA. It explains the trial setup process and why this specific setup has been chosen to effectively showcase all the features of both VQCM and DMA. In this blog, we have provided links to detailed step-by-step guides on configuring VQCM, complete with screenshots to guide you through the entire…
7 Game-Changing Use Cases for Self-Hosted Video Conferencing
7 Game-Changing Use Cases for Self-Hosted Video Conferencing Some things we know and never question. Birds fly. Fish swim. Dogs bark. You get the idea. Somewhere along the way, the world came to believe that when it comes to video conferencing, organizations have only two options – cloud or self-hosted (on-premises). This “one way or the other” concept may have been true 15 years ago when self-hosted video conferencing platforms were expensive…
Why Organizations Should Self-Host Video Conferencing
Why Organizations Should Self-Host Video Conferencing In today’s connected workplace, video conferencing is essential — not just for team collaboration, but for secure, day-to-day communication and mission-critical operations. While cloud-based platforms like Microsoft Teams, Zoom, and Google Meet dominate the market, they’re not always the right choice. For organizations that deal with sensitive data, strict regulatory requirements, or require full control over the data lifecycle, self-hosted video conferencing offers critical advantages. By running conferencing…
Not sure which VQ Communications products you need?
Our team is always happy to advise.
